- Messages
- 106
- Reaction score
- 0
- Points
- 26
Fluxion 3 link: https://github.com/FluxionNetwork/fluxion
= How it works =
- Scan for a target wireless network.
- Launch the Handshake Snooper attack.
- Capture a handshake (necessary for password verification).
- Launch Captive Portal attack.
- Spawns a rogue (fake) AP, imitating the original access point.
- Spawns a DNS server, redirecting all requests to the attacker's host running the captive portal.
- Spawns a web server, serving the captive portal which prompts users for their WPA/WPA2 key.
- Spawns a jammer, deauthenticating all clients from original AP and luring them to the rogue AP.
- All authentication attempts at the captive portal are checked against the handshake file captured earlier.
- The attack will automatically terminate once a correct key has been submitted.
- The key will be logged and clients will be allowed to reconnect to the target access point.
Requirements
A Linux-based operating system. We recommend Kali Linux 2 or Kali 2016.1 rolling. Kali 2 & 2016 support the latest aircrack-ng versions. An external wifi card is recommended.
-------------------------------------------------------------------------------------------------------------------------------------------------------------------
USB Compatible in Kali Linux:
TP-LINK TL-WN722N (Version 1 Only): http://ebay.to/2rSrDCk
Alfa AWUS036NH: http://amzn.to/2nqFk5T
Alfa AWUS036NHA: http://amzn.to/2sT0deZ
Panda PAU05: http://amzn.to/2FrxUH9
Alfa AWUS051NH: http://amzn.to/2rQpE1z
Alfa AWUS036NEH: http://amzn.to/2DLbXGu
Panda PAU09 (New): http://amzn.to/2uEcTYX
Alfa AWUS036ACH (New Drivers): http://amzn.to/2DPbCmm
Download Kali Linux here: https://www.kali.org/downloads/
====================================================================================================
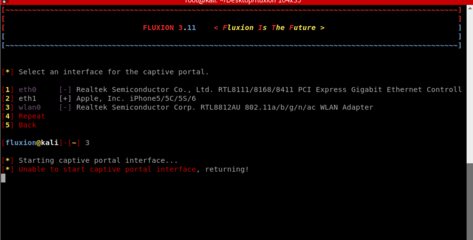
Instructions:
1. Make sure your usb wifi adapter was supported in Kali Linux so that you can enable the monitor mode & the fake AP.
2. Make sure you update & upgrade your kali linux before you can perform successfully the attacks of fluxion 3 copy this command in your terminal window > apt-get update -y && apt-get full-upgrade -y <
3. choose where do you to save the fluxion installer example > cd Desktop < & copy this command to download the fluxion 3 > git clone --recursive https://github.com/FluxionNetwork/fluxion.git <
4. change directory to fluxion folder type > cd fluxion <
5.change permission of your fluxion.sh copy this > chmod a+x fluxion.sh
6.run the fluxion.sh copy this > sudo ./fluxion.sh
For more info. Watch My Video Demo link below:
Please Don't Forget to SUBSCRIBE to My Channel: https://www.youtube.com/nxtechHacks For More Ethical Hacking Videos & Opensource router Setup & Configuration. Follow me on My FB: https://www.facebook.com/nxtechHacks/
View attachment 336265
(UPDATED 2018) VIDEO TUTORIAL HERE: https://youtu.be/WNskgqhXLL4

THANKS!
= How it works =
- Scan for a target wireless network.
- Launch the Handshake Snooper attack.
- Capture a handshake (necessary for password verification).
- Launch Captive Portal attack.
- Spawns a rogue (fake) AP, imitating the original access point.
- Spawns a DNS server, redirecting all requests to the attacker's host running the captive portal.
- Spawns a web server, serving the captive portal which prompts users for their WPA/WPA2 key.
- Spawns a jammer, deauthenticating all clients from original AP and luring them to the rogue AP.
- All authentication attempts at the captive portal are checked against the handshake file captured earlier.
- The attack will automatically terminate once a correct key has been submitted.
- The key will be logged and clients will be allowed to reconnect to the target access point.
Requirements
A Linux-based operating system. We recommend Kali Linux 2 or Kali 2016.1 rolling. Kali 2 & 2016 support the latest aircrack-ng versions. An external wifi card is recommended.
-------------------------------------------------------------------------------------------------------------------------------------------------------------------
USB Compatible in Kali Linux:
TP-LINK TL-WN722N (Version 1 Only): http://ebay.to/2rSrDCk
Alfa AWUS036NH: http://amzn.to/2nqFk5T
Alfa AWUS036NHA: http://amzn.to/2sT0deZ
Panda PAU05: http://amzn.to/2FrxUH9
Alfa AWUS051NH: http://amzn.to/2rQpE1z
Alfa AWUS036NEH: http://amzn.to/2DLbXGu
Panda PAU09 (New): http://amzn.to/2uEcTYX
Alfa AWUS036ACH (New Drivers): http://amzn.to/2DPbCmm
Download Kali Linux here: https://www.kali.org/downloads/
====================================================================================================
Instructions:
1. Make sure your usb wifi adapter was supported in Kali Linux so that you can enable the monitor mode & the fake AP.
2. Make sure you update & upgrade your kali linux before you can perform successfully the attacks of fluxion 3 copy this command in your terminal window > apt-get update -y && apt-get full-upgrade -y <
3. choose where do you to save the fluxion installer example > cd Desktop < & copy this command to download the fluxion 3 > git clone --recursive https://github.com/FluxionNetwork/fluxion.git <
4. change directory to fluxion folder type > cd fluxion <
5.change permission of your fluxion.sh copy this > chmod a+x fluxion.sh
6.run the fluxion.sh copy this > sudo ./fluxion.sh
For more info. Watch My Video Demo link below:
Please Don't Forget to SUBSCRIBE to My Channel: https://www.youtube.com/nxtechHacks For More Ethical Hacking Videos & Opensource router Setup & Configuration. Follow me on My FB: https://www.facebook.com/nxtechHacks/
View attachment 336265
(UPDATED 2018) VIDEO TUTORIAL HERE: https://youtu.be/WNskgqhXLL4


THANKS!
Attachments
Last edited: